How Fraudsters Use Bots to Bypass CAPTCHAs
Sanja Trajcheva
Cyber Risks & Threats
March 30, 2026
For attackers looking to access your website, a basic security test called CAPTCHA has been the first line of defense since its creation in 2000. In the decades since its inception, CAPTCHA has been the go-to method for stopping bots and keeping websites safe.
But the landscape has changed dramatically. Today’s threats are not just simple bots but fully automated AI agents capable of navigating pages, filling out forms, triggering CAPTCHA challenges, and routing them to solvers without human involvement. These agentic systems behave like automated browsers, complete with cursor movement, timing patterns, and human-like flow navigation.
As a result, CAPTCHAs are now both less effective at blocking bots and AI agents and more difficult for actual humans to complete.
Research now shows that a significant portion of CAPTCHA solves come from automated systems rather than real users. This creates a double bind: CAPTCHAs are less effective as a security layer while becoming increasingly frustrating for legitimate visitors. That means the attackers controlling the bots or agents can do everything from leaving spam comments and submitting invalid forms to abusing other services that your website provides.
The old model of “simple CAPTCHAs versus simple bots” is over. Understanding how modern automated agents get through these tests is critical for deciding whether CAPTCHA should still play a central role in your security strategy.
In light of this, now’s a good time to understand how CAPTCHA works, how a CAPTCHA solver can bypass it so easily, and what it means for your website.
What exactly is CAPTCHA?
CAPTCHA stands for “Completely Automated Public Turing test to tell Computers and Humans Apart,” and its core job is simple: let humans through, keep bots out.
In practice, CAPTCHA tests throw a small challenge in front of the user and ask them to prove they are human.
Most people are familiar with the typical types: misshapen or washed-out letters you have to retype, or grids of images where you’re told to select all squares containing a bus.
To pass, users simply enter what they see in the field provided. If the answer matches, they’re allowed into the protected area of the site.
Basic bots tend to misread the characters or click the wrong images, which makes them easy to filter out. The problem is that bots have evolved.
Advanced scripts now use AI, computer vision, and pre-training on huge libraries of examples to “read” distorted images almost as well as humans.
To combat this, more sophisticated systems like reCAPTCHA and hCAPTCHA add extra layers of complexity, mixing visual puzzles with behavioral signals to keep pace with increasingly capable bots.
Why are CAPTCHAs used?
CAPTCHA exists to protect websites from automated abuse. Any site that wants to restrict access from bots can implement it as a verification gate between human users and automated traffic.
The use of CAPTCHAs is widespread, and over 30 million websites rely on reCAPTCHA alone. You’ll often encounter them at key points in the user journey: before downloading a file, creating an account, submitting a form, or posting a comment.
For businesses, CAPTCHAs act as a simple but effective filter. They help block spam comments, prevent ticket scalping and form abuse, and reduce the risk of account takeovers by malicious bots attempting brute-force or credential-stuffing attacks.
In short, CAPTCHA adds friction for automation, protecting both the site and its users from low-level attacks that could otherwise flood or exploit public-facing pages.
Types of CAPTCHA
CAPTCHA is either text-based, picture-based, or sound-based, and the odds are that you’ve encountered all three.
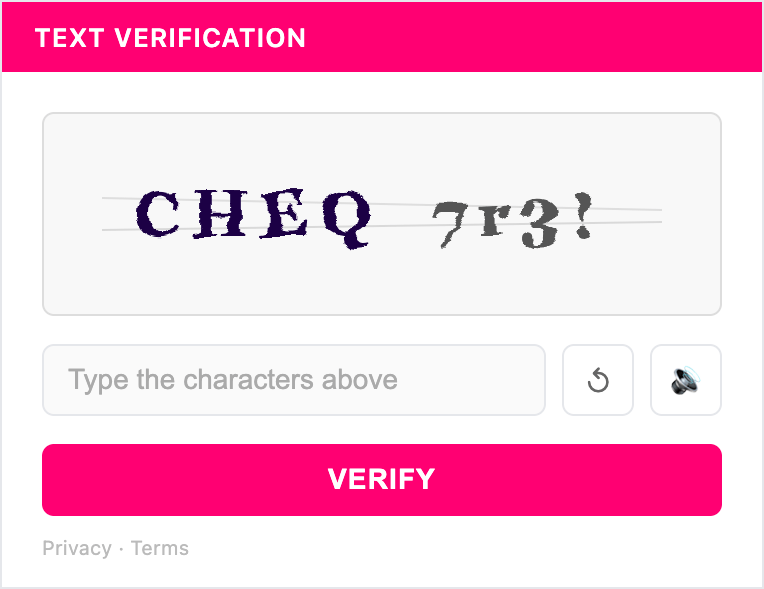
Text CAPTCHAs
These are the most common, and they require you to look at the distorted text to identify the real message. Sometimes they are actual words, and other times, they are plain gibberish distorted by shape, size, capitalization, or orientation.
The idea behind these wavy text images is to disrupt the way that computers ‘read’ images by breaking up any patterns that programs may have been trained to recognize as text. Think of it as camouflage for words.
If you fail enough text CAPTCHAs, you’ll usually get a prompt to attempt a different method of verification, like a CAPTCHA image.
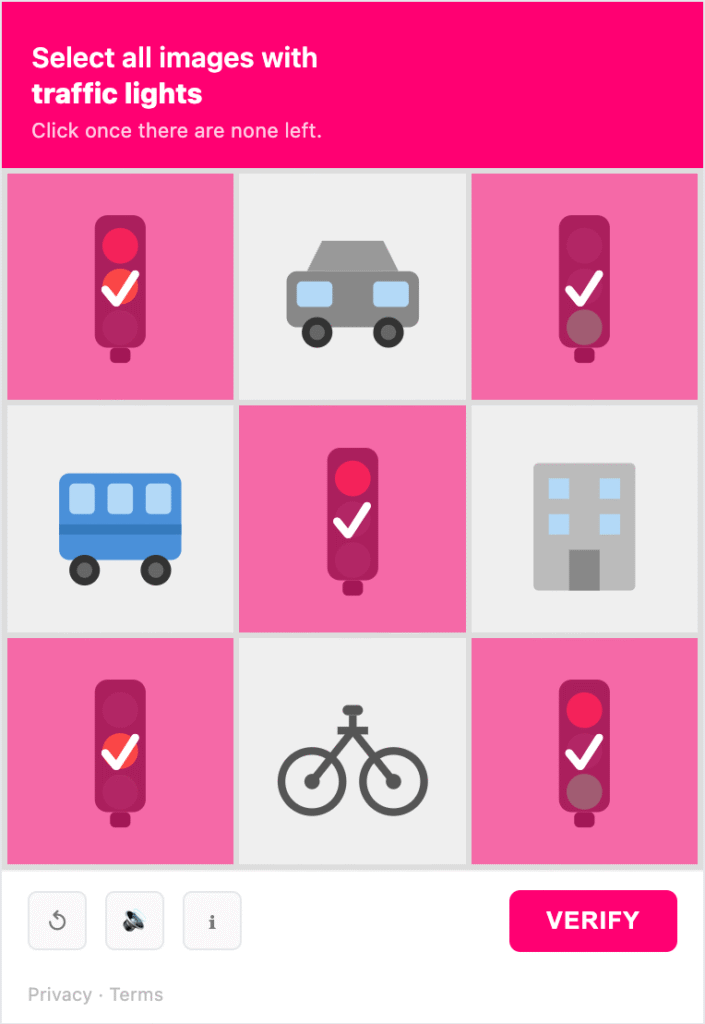
Picture CAPTCHAs
Image recognition-based CAPTCHA is another commonly used test that prompts the user to prove their humanity by correctly identifying sets of images or portions of a single image. ‘Click every tile with a crosswalk’ or ‘click every image containing a school bus’ are examples.
Computers have great difficulty detecting objects in images, and that kind of capability is hard to build and usually out-of-reach for botnets, so image CAPTCHAs are usually effective at keeping out bots. But while they do their job well, they’re also cumbersome and annoying for real users and can cause friction and even abandonment in the customer journey.
A CAPTCHA image can be quite troublesome when it doesn’t look like there’s a clear answer. Example: a picture where you have to select all the grids with traffic lights, even though the light is split between two grids.
Luckily, you can always hit the refresh button to get another image with zero consequences. Or, you could try the audio CAPTCHA.
Audio CAPTCHA
With audio CAPTCHAs, users can listen to a short recording and type the word they hear. These are effective because bots can’t use speech recognition to differentiate the pronounced characters from the background noise in the recording.
This can be time-consuming, especially compared to a text-based CAPTCHA, and can negatively affect both user experience and page-load times but audio CAPTCHAs are quite effective.
Behavior-based CAPTCHA: reCAPTCHA and hCAPTCHA
As bots have become more advanced, simple CAPTCHA tests and puzzles are no longer enough. Behavior-based CAPTCHAs, such as Google reCAPTCHA and its primary competitor, hCAPTCHA, add more complex functionality on top of the basic challenges.
These tools examine identifiers and behavioral data– how a user interacts with a webpage–to decide whether they are human. The classic example is reCAPTCHA’s “I’m not a robot” check box, which tracks mouse movements and other patterns to evaluate users.
If reCAPTCHA believes a user is human, they are presented with the simple checkbox test. If they are suspected to be a bot, they may instead see a more difficult image-based test.
By providing different tests based on contextual clues, behavior-based CAPTCHAs aim to reduce friction for most users while still providing tougher verification for suspicious traffic.
However, these tools are still susceptible to advanced bots and CAPTCHA-solving services, and they come with their own set of difficulties.
Google’s offering, for example, can cause privacy concerns. ReCAPTCHA gathers device, software, and behavioral data, some of which may be used for purposes beyond security.
hCAPTCHA takes a different approach and does not rely so much on user data, but as a result, it is more likely to present human users with complex challenges.That can be quite frustrating and can add an undesirable amount of friction to a landing page.
How do CAPTCHAs affect user experience?
The clear benefit of CAPTCHA is that it keeps out many common, simple bots, but that protection comes with real costs for legitimate users.
CAPTCHAs–especially difficult ones–can be very disruptive to user experience. They may be difficult for certain audiences to use or understand, resulting in a high rate of false positives and page abandonment.
CAPTCHAs are much more disruptive for mobile users, who are more likely than desktop users to leave a website when they are challenged.
CAPTCHAs were designed to stop early-generation bots that struggled with distorted text or basic image recognition. But modern AI agents navigate the web like lightweight autonomous browsers, making CAPTCHA challenges far easier to defeat.
AI agents can solve traffic-image and grid-style CAPTCHAs with up to 100 percent success rate, often matching or outperforming humans.
How do hackers bypass CAPTCHA?
Hackers now have a much easier time getting around normal CAPTCHA challenges, and they use a mix of automation, tooling, AI agents, and even human labor to do it.
How AI Image and Audio Recognition Is Used to Crack CAPTCHAs
In his book Deep Learning for Computer Vision with Python, Adrian Rosebrock lays out his strategy for bypassing CAPTCHA on the E-ZPass New York website. His approach included downloading hundreds of example images to train his system because he didn’t have access to the source code and then releasing the learned AI on the system.
CAPTCHAs with an open source code are, in theory, easier to crack because hackers can use the source to train their machine learning system to bypass CAPTCHA tests, regardless of the difficulty. Anybody can pass the exam if you know all the possible questions.
Today, attackers no longer need to build everything from scratch. Modern agentic tools can simply screenshot CAPTCHAs and route them to vision models or external solvers that handle both text- and image-based tests.
Common Technical Strategies Attackers Use to Bypass CAPTCHA
Hack Tricks lists some of the ways that hackers get around CAPTCHA easily. Some of them include checking your page’s source code for CAPTCHA solutions (in case it’s text) or using an old CAPTCHA value in case they get the same challenge twice.
Other CAPTCHA bypass strategies include:
- Using optical character recognition (OCR) to read the characters on the screen
- Checking how many images are being used and detecting them with MD5
- Sending the CAPTCHA parameter empty and seeing if that does the trick.
Browser Extensions and APIs
Browser extensions such as Buster are marketed as tools to help human users solve annoying or difficult CAPTCHA verification challenges, but they can easily be leveraged by bots. Even innocuous APIs can be used, for example, Google’s reCAPTCHA allows users to download audio files, which can then be solved with Google’s own Speech Recognition API.
CAPTCHA solving services and click farms
For hackers who don’t want to develop their own solutions for CAPTCHA challenges, there are a plethora of solutions available that will help them bypass checks for astonishingly low costs. These range from CAPTCHA-solving APIs leveraging sophisticated AI tools to click farms that hire large numbers of human workers to manually solve CAPTCHA challenges.
These ‘CAPTCHA Farms’ leverage simple APIs that allow a client bot to call the service when it encounters a CAPTCHA. Workers solve the CAPTCHA in real time and send the response token back to the bot, which then continues its attack.
These workflows are now often embedded directly into AI-agent pipelines, combining automated browsing with human-in-the-loop CAPTCHA solving to maintain uninterrupted attack flows.
How Security Vulnerabilities in reCAPTCHA Have Enabled CAPTCHA Bypass
In 2018, a security researcher found a bug that allowed him to bypass Google’s reCAPTCHA. The basic gist is that web apps using reCAPTCHA have to create the request in a specific way, and sometimes, the request is insecure. When this happened, attackers could bypass the reCAPTCHA every single time. (Andres Riancho)
The bug has since been patched, and it’s no longer possible to recreate the reCAPTCHA bypass. However, this is a prime example of how attackers can exploit bugs and weaknesses to bypass your site’s CAPTCHA.
| Bypass Method | How It Works | Attacker Tooling |
|---|---|---|
| AI Image & Audio Recognition | Trains vision and audio models on CAPTCHA examples to solve challenges automatically — no human involvement required | Computer vision models, ML frameworks, pre-trained solver libraries |
| Technical Exploit Strategies | Checks page source for exposed CAPTCHA solutions, reuses old CAPTCHA tokens, or submits empty CAPTCHA parameters | OCR tools, MD5 image detection, source code inspection |
| Browser Extensions & APIs | Extensions marketed as accessibility tools are repurposed by bots; audio CAPTCHA files are routed to speech recognition APIs for automated solving | Buster browser extension, Google Speech Recognition API |
| CAPTCHA-Solving APIs | Third-party services accept an unsolved CAPTCHA challenge and return the solved token in real time, which the bot uses to continue its attack | Commercial CAPTCHA-solving API services |
| Click Farms | Human workers are paid to solve CAPTCHAs at scale for very low cost per solve, providing a cheap pipeline for high-volume attacks | Farm APIs, human labor networks |
| Agentic Pipelines | Modern AI agents combine automated browser navigation with CAPTCHA-solving services end-to-end, maintaining uninterrupted attack flows with no human in the loop | AI agent frameworks, automated browser tools, integrated CAPTCHA-solving APIs |
What happens when hackers crack your CAPTCHA?
Any attacker can get past your CAPTCHA by solving it as a human would, but the real danger begins when they can bypass it at bot scale. At that point, they can bombard your server with requests, overload resources, and potentially steal data.
Increased spam
Without an effective CAPTCHA “gatekeeper,” you can expect spam comments that advertise everything from malicious services to other websites.
If your website requires manual approval, the public may never see these comments, but your team can be buried under dozens or hundreds of irrelevant submissions.
Invalid analytics data
Bots will skew the traffic on your web page and render your analytic data useless. If hackers get past your CAPTCHA, you might see a spike in visits with zero conversions or abandoned carts and have no clear explanation why.
Insecure shopping checkout
If you own an eCommerce website, a bypassed CAPTCHA means that hackers can now access user accounts, make purchases with stolen cards, and even access other sensitive areas of your website.
Database access
If you don’t have CAPTCHA set up for your website login, then you might want to consider adding it. Bots can be used to access poorly secured user accounts and perform account takeovers. They can also access your online databases and even perform other forms of content-based fraud on your site.
Fewer web resources
With access to your website, bots will bombard your website, submitting connection requests and taking up finite resources. That means that legitimate users will have slowed or even nonexistent access to your website, which can be damaging to your business. Research shows that 53% of people will go to a competitor if your website takes longer than 3 seconds to load.
What can you do about CAPTCHA bypassing bots?
CHEQ bot mitigation adds an additional layer of security to your website, stopping the most common forms of automated traffic from accessing your site. The service scans your visitor activity for telltale signs of bot presence and blocks them from interacting with your website.
That means even if they get through your CAPTCHA, a bot mitigation solution will identify and purge them from your website, allowing only genuine customers to reach your forms, checkout, and content.
Protecting Forms Without CAPTCHAs
CAPTCHAs still help against simple automation, but they provide little resistance against modern AI agents and come at a real cost to user experience. If your forms or checkout flows rely solely on CAPTCHA for protection, you are likely frustrating legitimate customers more than you are stopping serious threats.
A more effective, user-friendly approach is to use form protection that works invisibly in the background. CHEQ Form Guard shields your forms and go-to-market funnel from bots and fake users that drain resources, create sales-marketing tension, erode trust, and introduce privacy and reputational risks. Rather than interrupting real users with puzzles, Form Guard stops junk leads before they enter your systems.
By blocking invalid and malicious submissions before they sync to sales teams or marketing platforms, Form Guard:
- Prevents fake form submissions that waste rep time
- Protects email and retargeting performance from bot-contaminated data
- Defends high-value CTAs from exploitation
- Preserves clean segmentation across marketing platforms
- Maintains the integrity of your go-to-market funnel
- Protects real user privacy preferences
- Supports compliance while preserving a clean, trustworthy pipeline
Final Thoughts
CAPTCHAs may still stop some basic automation, but they are no longer enough to meaningfully protect forms, funnels, or user accounts. AI agents can solve or bypass most CAPTCHA formats at scale, while legitimate visitors increasingly bear the burden of complex challenges.
If your protection strategy relies on CAPTCHA difficulty, the tradeoff becomes clear: automation keeps improving while human experience keeps degrading. A more modern, realistic approach treats CAPTCHA as only one small signal in a broader defense strategy.
CHEQ Form Guard provides the kind of protection today’s funnel actually requires. By blocking fake and malicious submissions before they enter your systems, it preserves sales productivity, protects marketing effectiveness and efficiency, and minimizes privacy and compliance risk.
In an environment where agentic automation is accelerating, securing forms without adding friction for real users isn’t just preferable. It is essential.
To safeguard forms and customer journeys in a world of agentic automation, you need solutions built for how bots work today, not how they worked a decade ago.
Get started with a CHEQ Form Guard demo today.